A new hire sits down on day one, opens the welcome email, clicks the training link, and hits a login error. HR thinks onboarding has started. The employee thinks the company isn’t organised. That gap matters more than many organizations acknowledge.
A talent management system login isn’t just a gate in front of software. It’s the first interaction many employees have with performance goals, mandatory training, career paths, feedback cycles, and development records. When access is smooth, people get moving. When it isn’t, everything behind the login page feels harder than it should.
Why Your TMS Login Process Matters More Than You Think
The login screen shapes employee experience early. If users can’t get in quickly, they don’t just lose a few minutes. They miss orientation tasks, delay compliance training, skip profile setup, and start associating your talent systems with friction.

That’s why I treat login design as part of talent strategy, not just system administration. Organisations optimising their talent management system login processes have reported a 35% increase in employee engagement, according to a 2022 study highlighted in industry analyses, as noted by the Talent Management Institute overview of TMS login access.
What the login actually controls
The login page is often the doorway to work that directly affects retention and performance:
Onboarding access: New starters need one place to complete forms, review policies, and start required learning.
Performance visibility: Managers and employees use the system to review goals, check progress, and prepare for conversations.
Development activity: Training plans, certifications, and internal mobility options all depend on reliable access.
Manager confidence: If leaders can’t get to dashboards or review cycles easily, adoption drops fast.
Practical rule: If an employee needs to ask where to log in, which password to use, and whether MFA is required, the process is already too complicated.
A good platform can connect learning, development, and workforce data well, but that value only appears after people get through the front door. If you’re evaluating the broader role of these platforms, this guide to talent management system software is a useful starting point.
Finding and Using Your Company's TMS Login Page
Most login issues start before anyone types a password. Users are often on the wrong page, using the wrong sign-in method, or trying an old bookmark from a prior system.
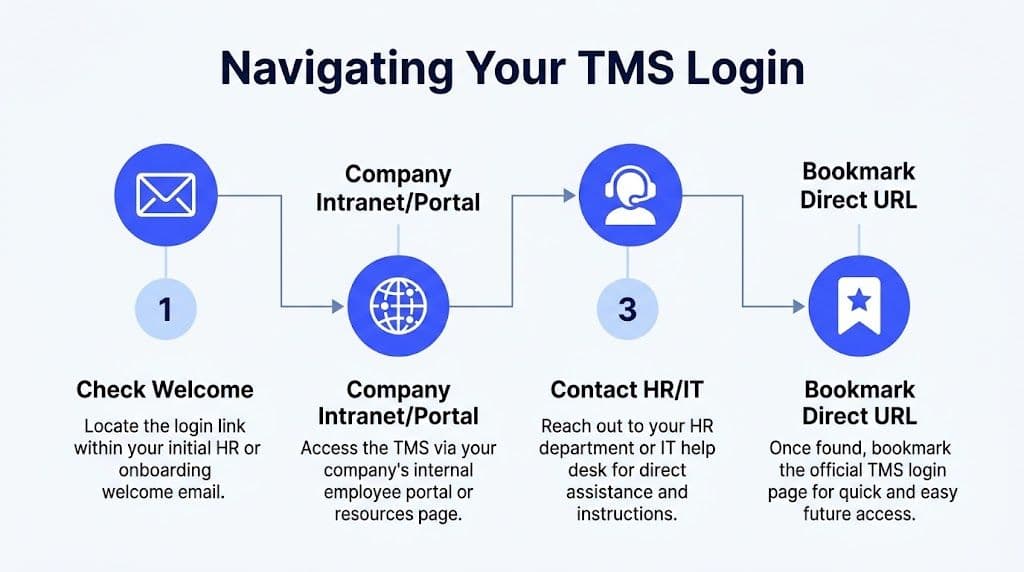
Where to look first
Use this order. It solves most first-time access problems.
Check your welcome email. HR or onboarding usually sends the correct login URL and tells you whether you’ll use SSO or a separate password.
Search the company intranet. Many organisations place the TMS under employee resources, learning, HR systems, or onboarding.
Ask HR before IT if you’re new. HR usually knows whether your account has been provisioned yet.
Bookmark only the final verified page. Don’t bookmark a redirect page unless your company tells you to.
For teams using a documented setup process, the Learniverse quick start guide shows the kind of clear access flow that reduces first-login confusion.
If your company uses SSO
Single Sign-On (SSO) means you sign in with an existing company identity, often Microsoft or Google. This is usually the cleanest option because users don’t need to remember another password.
Use the same company account you use for email, not your personal account. That’s the mistake I see most often with Google-based sign-ins.
Common SSO flow:
You open the TMS login page.
You click Sign in with Microsoft or Sign in with Google.
The identity provider checks your credentials.
If your company has security policies enabled, you complete MFA.
You land in the TMS dashboard or homepage.
SSO works well because account lifecycle management is simpler. When IT updates a role or disables an account, access follows that identity. It’s cleaner than managing disconnected usernames.
A short demo can help if your team is visual. This walkthrough covers a typical access flow:
If your company uses username and password
Some organisations still use a direct TMS account. That can work fine, but only if setup is handled carefully.
Watch for these basics:
Use the exact username format provided. It may be your work email, employee ID, or a generated username.
Set your password once, then save it properly. A password manager is safer and less error-prone than reusing an old password.
Complete activation promptly. First-time links often expire or become invalid after one use.
Don’t create duplicate accounts. If the system says your email already exists, stop and ask support to confirm your profile status.
If the page offers both SSO and local login, don’t guess. Your company almost certainly expects one path, not both.
Mastering Multi-Factor Authentication (MFA)
MFA frustrates people when it’s introduced badly, but it prevents larger headaches. A TMS contains sensitive employee information, performance records, learning histories, and sometimes recruitment data. Protecting that access matters.

For CA-based SMBs and franchises, TMS login optimisation via AI-driven adaptive authentication yields a 35% reduction in time-to-fill positions, partly by securing the candidate and employee data that powers these systems, according to FlowHCM’s talent management metrics discussion.
Choose the least painful MFA method that still fits your risk level
Not all MFA methods feel the same in daily use.
Authenticator apps are usually the most dependable for regular employees.
Push notifications are easier for non-technical users because they only need to approve or deny a prompt.
SMS codes are familiar, but they often create avoidable support tickets.
Security keys suit higher-security environments, though setup needs stronger admin support.
If your HR stack already uses identity tools across leave, training, and employee systems, reviewing a practical Okta integration example can help you think through how access should stay consistent across platforms.
What good MFA setup looks like
A clean rollout usually includes:
One clear enrolment email with screenshots or exact prompts.
A backup method in case the primary device is unavailable.
Recovery instructions that don’t require the locked-out user to guess who owns the reset process.
A short explanation of why MFA is required, written in plain language.
MFA should add one confirmation step, not a support maze.
If someone loses their phone, the right move isn’t to keep retrying. They should contact the named admin or service desk, verify identity through the approved process, and re-enrol on the replacement device. Teams get into trouble when they improvise recovery instead of following a controlled reset.
Troubleshooting Common TMS Login Issues
When users say “the system is down”, the problem is usually narrower. It’s often a browser issue, a mismatched login path, an expired code, or an account state problem. The fastest way to resolve it is to identify the symptom before escalating.
Common Login Error Fixes
Error Message / Symptom | Likely Cause | How to Fix It |
Incorrect username or password | Wrong username format, saved old password, or accidental typo | Re-enter credentials slowly. Check whether the username should be your work email or employee ID. If a password manager auto-filled the wrong entry, delete that saved record and try again. |
SSO sign-in keeps looping back to login page | You’re on the wrong login route, or the browser has stale session data | Return to the official company login page, close duplicate tabs, then clear browser cookies for the site or try a private browsing window. |
MFA code doesn’t work | Code expired, phone time is out of sync, or the wrong MFA method was selected | Request a fresh code, confirm the correct authenticator account is being used, and check device time settings if using an authenticator app. |
Account locked after repeated attempts | Too many failed sign-in attempts triggered a security lockout | Stop trying random combinations. Wait for the lockout period if your policy allows it, or contact the admin named in your onboarding message for a reset. |
Password reset email never arrives | Email delay, spam filtering, or the account isn’t fully provisioned | Check junk and quarantine folders, then confirm with HR or IT that the account was created and linked to the correct email address. |
Login works on one browser but not another | Browser extension conflict or cached page issue | Disable privacy or password extensions temporarily, update the browser, or switch to a supported browser approved by your company. |
You can log in but see no courses or tasks | Access rights are incomplete or your role assignment hasn’t been applied | Contact the system administrator with your manager name, department, and expected access so they can review role mapping. |
What to try before opening a ticket
A useful support ticket starts with a few checks already done:
Confirm the page URL: Make sure you’re using the official login page, not a stale bookmark.
Test another browser: If Chrome fails, try Edge or Safari depending on company support standards.
Capture the exact error text: “It doesn’t work” slows everything down.
Note whether others can sign in: That tells support whether it’s a user issue or a broader outage.
A screenshot of the full error page, plus the time it happened, usually cuts resolution time more than a long email description.
If your organisation has a support knowledge base, keep the user-facing instructions short and centralised. A simple resource like the getting started FAQ is the right model. Users shouldn’t need to search across five documents to reset a password.
An Admin's Guide to Managing User Access and Recovery
Admins influence adoption long before the first employee signs in. Most login pain comes from weak provisioning, vague communications, and recovery processes that live only in one person’s head.
Build access into onboarding, not after it
A reliable rollout has a few essential requirements:
Provision accounts before start date. Don’t wait until the employee is already asking for help.
Send one welcome message with one login route. Mixed instructions create duplicate tickets.
State the support owner clearly. Users need to know whether HR, IT, or a vendor manages resets.
Assign the right role from day one. Successful login with empty access still feels broken.
When I audit these workflows, the strongest teams treat access as part of the onboarding checklist owned jointly by HR and IT. Neither team can assume the other handled it.
Recovery should be controlled and fast
Password resets and MFA resets need an approved playbook. Keep it simple enough for support staff to follow consistently.
A strong recovery flow usually includes:
Identity verification through the approved internal process.
Reset of the failed factor, not the whole account unless necessary.
Forced re-enrolment for MFA if a device is lost or replaced.
Confirmation to the user with exact next steps and timing.
Test login journeys before launch
Often, teams cut corners in this area and face repercussions later. In Canadian organisations, a step-by-step User Acceptance Testing (UAT) methodology for TMS login workflows achieves 92% adoption rates within 90 days post-launch, according to APQC benchmark data cited in the TMI guide to choosing a talent management system.
That result makes sense. Login workflows should be tested by real users, not just admins who already know the shortcuts.
Test these scenarios before release:
New hire first login
Manager access to team dashboards
Password reset from a mobile device
MFA enrolment and recovery
Role changes after promotion or department transfer
If you’re selecting tools, keep the experience unified. For example, Learniverse supports sign-in with Google, email and password, or guest access, which is useful when training teams need different access modes for employees and external learners.
FAQs on Advanced TMS Login Topics
How do I make a TMS login page accessible?
Accessibility can’t be an afterthought. A key underserved angle in talent management system login content is the lack of guidance on accessibility compliance for disabled users under ADA and California-specific AB 434, which mandates WCAG 2.1 AA standards, as noted in the VA TMS SecureAuth reference. In practice, that means testing keyboard navigation, visible focus states, screen reader labels, error messaging, colour contrast, and timeouts that don’t trap users.
What should HR consider when MFA intersects with privacy rules?
Keep the method proportionate to the risk. Collect only the information needed to verify access, document who can see it, and work with legal or privacy teams before introducing biometric or device-based factors. The safest approach is usually the one employees can understand and support can explain.
How should contractors and temporary staff be handled?
Don’t force them into the same access model as permanent staff if their needs differ. Give them time-bound accounts, role-limited permissions, and a clear offboarding trigger. The login should match the work they need to do, nothing more.
If your team wants a simpler path from login to learning delivery, Learniverse is one option to consider. It lets training teams turn source materials into courses, provide a branded portal for access, and manage learner sign-in through common methods such as Google or email-based accounts, which can reduce friction between account access and actual training completion.